which I intentionally don't emphasized.
blog.darkstar.work - a simple url encoder/decoder
Labels
2023-10-22
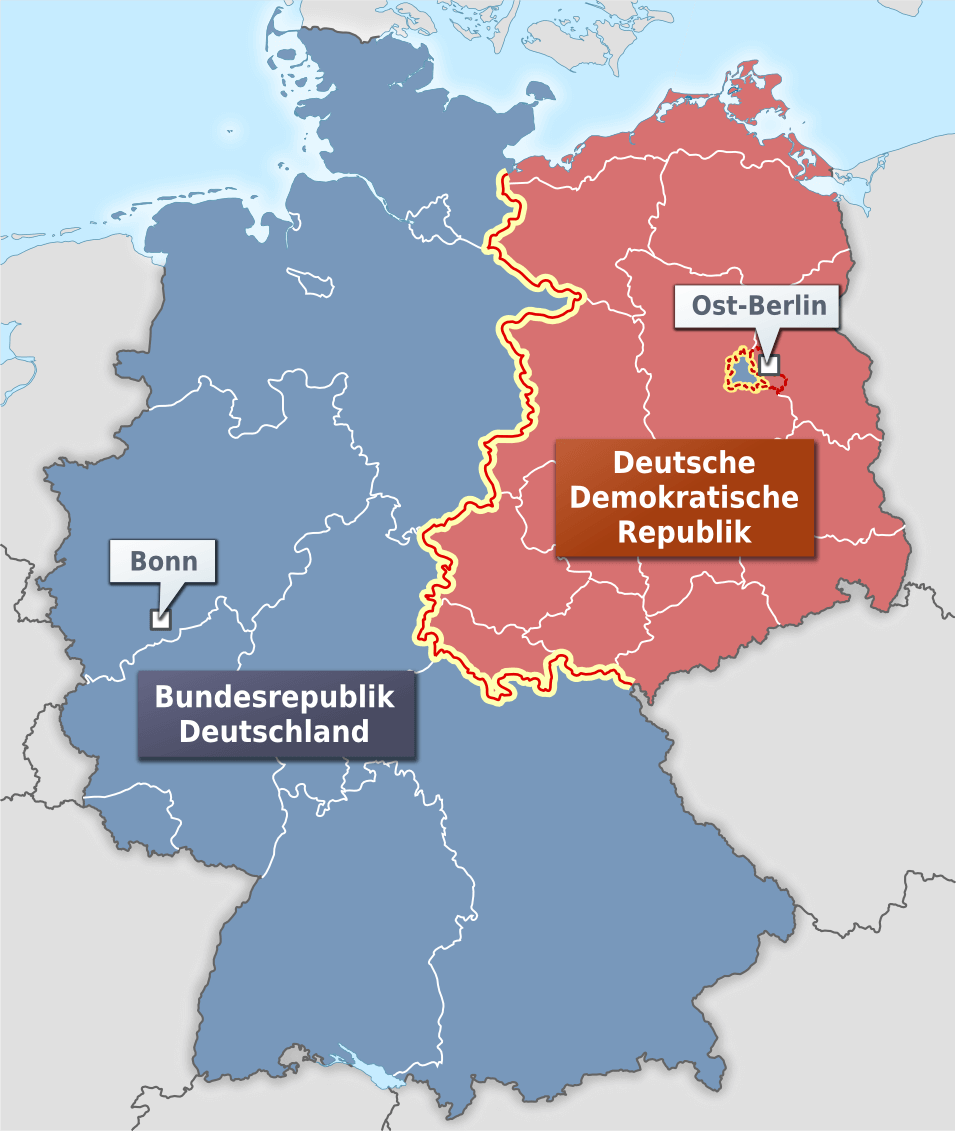
Case study of apparently sowiet (U.S.S.R.) tactical advantages during cold war (20th century)
which I intentionally don't emphasized.
2023-10-17
Erfahrungsbericht zur Psychiatrie, Psychotherapie, angewandten Psychologie und psychosozialen Diensten
1. Psychiatrie
1.1. geschlossene Abteilung der Psychiatrie
In manchen Fällen gelten Patienten auf der geschlossenen Station rechlich als nicht mündig | entscheidungsfähig | geschäftsfähig.
1.2. offene Abteilung der Psychiatrie
Der Entlassung aus der offenen Abteilung der Psychiatrie muss entweder
- hoher Qualitätsstandard
eine Untersuchung eines Arztes | einer Ärztin und eines Pflegers | einer Pflegerin und einer neutralen Verwaltungsperson der Klinik vorangehen (
- mittlerer Qualitätsstandard
eine Untersuchung zumindest eines Arztes | einer Ärztin
Bei der Entlassung aus der Psychiatrie wird meist eine Depotspritze oder andere regelmäßig einzunehmende Psychopharmaka als Reszept verschrieben.
2. Psychotherapie (angewandte Psychologie)
Ich nenne dafür einige Beispiele:
3. Psychosoziale Dienste
2023-10-15
ATX and austrian stock market traded companies
2023-07-29
Snow White Spinderula waked up after corona crisis, 7 dwarfs arround her and a lot of things disappeared
There was a girl named "Snow White Spinderula", who awaked from a stunned, cryostatic, petrified, paralyzed state, because she ate the forbidden fruit of knowledge from the apple tree in the garden of paradise and a piece of apple got stuck in her throat.
Snow White Spinderula spits out the piece of apple, breathes and feels permeated again by the fresh and active spirit of life, recognizing that 7 dwarves standing around her.
Bit by bit she realizes now that many different things in the current world have disappeared or gone for ever and that this had nothing at all to do with the 7 dwarfs keeping an eye on her.
Disintegrated, disappeared, died ot transformed to void
Feminist internet blogs, groups and communities in social media
Small left parties, autonomous groups and comunity based projects

A lot of internet media blogs in right, conservative and liberal spectrum were gone
Also a lot of conservative, right wing and liberal blogs moved to virtual graveyard also known as /dev/null or Nirvana.
It's sad to see many blogs from reasonable moderate-citizen first disappeared and in result of that disappearance many rescrictions by law were made against "more radical" groups:
It's so sad to realize, that so many groups from the left or middle-class spectrum of society disappeared, shut down their internet presence and blogs and let themselves be pushed out and no longer dared to express their opinion freely in public space or on main stream channels of the internet.
A lot of things concerning software, system and kernel programming
Some very passionate discussions in the linux kernel newsgroup between Linus Torvalds and Alan Cox concerning sync before close, fbarrier as alternative to fsync with funny swipes to Alans work at Intel and drinking same kool-aid as other hardware cpu programmers.
Integration of NIS (Network Information Sytem originally called Yellow Pages) in latest apple OS.
Some projects on freshmeat.net sourceforge.net knowledge to use UDP for large - huge amount of data and the intention to develope a symmetric, asymmetric or certificate based standardized encryption for all services based on UDP.
Realization that everything (file transfer, authentication, authorization including claims and bearer tokens, web services instead of old style Sun RPC or modern gRPC, VPN, ...) over HTTPS might not be always the ideal solution and best practice and could be realized more service oriented otherwise.
Development of a more reliable driver and toolkit for mounting btrfs, ext2-4, xfs zfs file systems under Microsoft Windows 10-11.
or maybe not?Full capacity of steel processing industry at voestalpine
Full capacity of stell processing industry at voestalpine Linz
https://www.voestalpine.com/highperformancemetals/international/en/
A Gothic Madonna replaced by a fake (both the original and the fake)
Photo of faked gothic madonnaMany other things will be reported soonly
Many other things will be reported soonly.
2023-07-14
companies & software in scope of DNA genetic engineering

It is up to everyone to evaluate the opportunities and risks after exploring and learning the scope and hardfacts in detail.
- CloneManager [ www.scied.com/pr_cmpro.htm |
clone-manager-professional.software.informer.com ] - DNADynamo BlueTractorSoftware [ www.bluetractorsoftware.com ]
- DNASTAR [ www.dnastar.com/software/lasergene/ ]
- Eclipsebio [ eclipsebio.com ]
- Genomelink [ genomelink.io ]
- QIAGEN CLC Genomics Workbench Premium
- SnapGene [ www.snapgene.com ]
[ ... to be continued ... ]
2023-06-30
VIC20 Emulatoren
In einem Anfall von Nostalgie lud ich mir 2 VIC20 Emulatoren herunter.
und programmierte in BASIC ein einfaches Zahlenratespiel:
2023-06-17
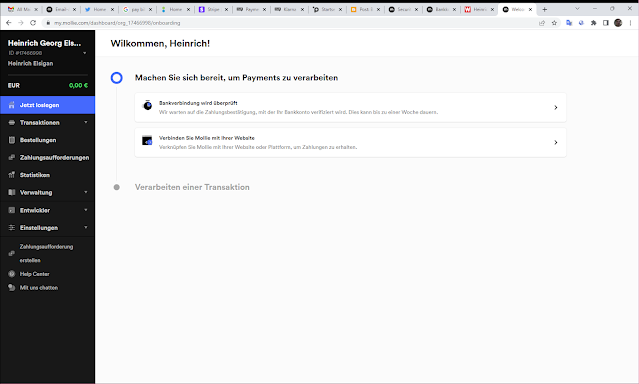
Payment & Billing online provider services
PayPal
Klarna

Planet Payment
Stripe / payments
Mollie
2023-06-02
Commercial business livestyle, NPO and the few community based lifestyle, that we ignore
Common images in western societies from social and economic point of view:
Family (classic)
At least one or both parents work most of the year and gain income for family. Family might get money from the state for the children to help getting them educated in public or private school and later an education to get a paid job in our economy.
Pair of adults (might be even gay or lesbian)
A pair in a kind of love or sexual relation lives together, because they cannot reproduce or don't want to have children. Normally both work (maybe not fulltime) and earn money.
Single adult (might be divorced father)
Forgotten community based live styles
- extended family (were some of the members receive money in form of social benefits or unemployment insucrance from state, insucrances or relatives, could be clan based)
- spiritual or far left community (e.g. new age group, marxists, trotskyists, like-minded community)
- [Please enter you own expiriences here]
Misunderstandings and conflicts concerning community based live forms
- It is a mistake to assume that all community based lifestyles are voluntary, often it is economic pressure that leads to such living conditions.
- But it is also wrong that nobody wants to live like this and people who live like this need education upgrades or training positions to enter jobs.
- Since community-based forms of life are mostly sustained by money that is not entirely self-earned, there is often the argument that they take it away from the really old and weak or disabled because it is mostly spent by the state.
- Community based persons never understand the importance that somebody is stressed and races to an urgent meeting with an important wealth customer.
- On the other hand, working people with functioning business models do not understand the obligations of community-based individuals, who often donate odd amounts of time to unnecessary inefficient rituals within the community.
- Community based lifestyles are often viewed as precariously archaic or uncivilized, although the rules or code in such communities are often very complex, but often inhibit individuals from their full economic capacity or individual self-expression.
2023-05-09
Supu (Sudoku Puzzle) by Georg Toth
Hi, I implemented SUPU (SUdoku PUzzle), idea & design by Georg Toth for Windows Desktop.
You can order Supu on Georg Toth Webshop here:
https://www.georg-toth.com/supu
2023-01-20
frogA - frogger Adroid
so a little fun project "frogA- frogger Android" is taking some little progress.
https://github.com/heinrichelsigan/frogA/releases
Git repository:
https://github.com/heinrichelsigan/frogA
lastest build APK package:
https://github.com/heinrichelsigan/frogA/releases/download/v1.2.24.6-2023-02-02/frogA_v1_2_24_6-2023-02-02-debug.apk

https://www.youtube.com/shorts/4FAhYn2c5oU
2022-11-29
flex - fast lexical analyzer generator sample
Orginal posting can be fount here: http://blog.darkstar.work/2012/05/flex-fast-lexical-analyzer-generator.html
Who remember flex: fast lexical analyzer generator?
Here is a short sample, I have written it under gnu linux and ported it to win32 using gnuwin32 flex and getoptwin:
2022-11-15
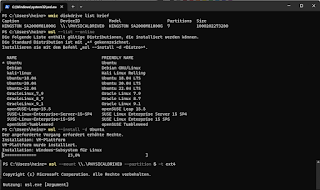
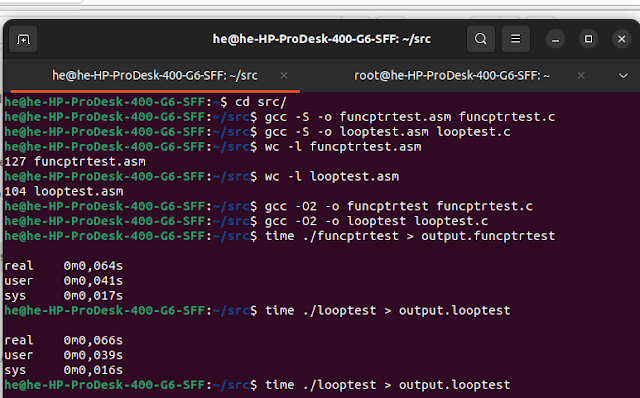
Could too much function pointers (delegates) inside many huge loops have an effect of unoptimizable code?
We have this simple c modified code from stack overflow called funcptrtest.c:
include <stdio.h>
/* C code for program funcptrtest.c
=> https://pastebin.com/rUtXfgSG
*/
const int b = 23;
// A normal function with an int parameter and void return type
void fun(int a)
{
if (a < b)
printf("Value of a (%d) is lesser then value of b (%d)\n", a, b);
else if (a == b)
printf("Value of a (%d) is equal value of b (%d)\n", a, b);
else if (a > b)
printf("Value of a (%d) is greater than value of b (%d)\n", a, b);
}
// main => NO KNR style int main(argc, argv) int argc; char **argv
int main(int argc, char **argv)
{
int i = 0;
/* fun_ptr is a pointer to function fun()
void (*fun_ptr)(int) = &fun;
is equivalent of following two
void (*fun_ptr)(int);
fun_ptr = &fun;
*/
void (*fun_ptr)(int) = &fun;
// call once with static int
(*fun_ptr)(b);
// iterate through for loop
for (i = 1; i < 101; i+=11) {
// Invoking fun() using fun_ptr
(*fun_ptr)(i);
}
return 0;
}
We compile it now with gnu c compiler with gcc option -S and generate an assembler file:
gcc -S funcptrtest.c -o funcptrtest.asm
Result will be something like this:
.file "funcptrtest.c"
.text
.globl b
.section .rodata
.align 4
.type b, @object
.size b, 4
b:
.long 23
.align 8
.LC0:
.string "Value of a (%d) is lesser then value of b (%d)\n"
.align 8
.LC1:
.string "Value of a (%d) is equal value of b (%d)\n"
.align 8
.LC2:
.string "Value of a (%d) is greater than value of b (%d)\n"
.text
.globl fun
.type fun, @function
fun:
.LFB0:
.cfi_startproc
endbr64
pushq %rbp
.cfi_def_cfa_offset 16
.cfi_offset 6, -16
movq %rsp, %rbp
.cfi_def_cfa_register 6
subq $16, %rsp
movl %edi, -4(%rbp)
movl $23, %eax
cmpl %eax, -4(%rbp)
jge .L2.L2:
movl $23, %eax
cmpl %eax, -4(%rbp)
jne .L4
movl $23, %edx
movl -4(%rbp), %eax
movl %eax, %esi
leaq .LC1(%rip), %rax
movq %rax, %rdi
movl $0, %eax
call printf@PLT
jmp .L5
.L2:
movl $23, %eax
cmpl %eax, -4(%rbp)
jne .L4
movl $23, %edx
movl -4(%rbp), %eax
movl %eax, %esi
leaq .LC1(%rip), %rax
movq %rax, %rdi
movl $0, %eax
call printf@PLT
.L2:
movl $23, %eax
cmpl %eax, -4(%rbp)
jne .L4
movl $23, %edx
movl -4(%rbp), %eax
movl %eax, %esi
leaq .LC1(%rip), %rax
movq %rax, %rdi
movl $0, %eax
call printf@PLT
jmp .L5
.L4:
movl $23, %eax
cmpl %eax, -4(%rbp)
jle .L5
movl $23, %edx
movl -4(%rbp), %eax
movl %eax, %esi
leaq .LC2(%rip), %rax
movq %rax, %rdi
movl $0, %eax
call printf@PLT
.L5:
nop
leave
.cfi_def_cfa 7, 8
ret
.cfi_endproc
.LFE0:
.size fun, .-fun
.globl main
.type main, @function
main:
.LFB1:
.cfi_startproc
endbr64
pushq %rbp
.cfi_def_cfa_offset 16
.cfi_offset 6, -16
movq %rsp, %rbp
.cfi_def_cfa_register 6
subq $32, %rsp
movl %edi, -20(%rbp)
movq %rsi, -32(%rbp)
movl $0, -12(%rbp)
leaq fun(%rip), %rax
movq %rax, -8(%rbp)
movl $23, %edx
movq -8(%rbp), %rax
movl %edx, %edi
call *%rax
movl $1, -12(%rbp)
jmp .L7
.L8:
movl -12(%rbp), %eax
movq -8(%rbp), %rdx
movl %eax, %edi
call *%rdx
addl $11, -12(%rbp)
.L7:
cmpl $100, -12(%rbp)
jle .L8
movl $0, %eax
leave
.cfi_def_cfa 7, 8
ret
.cfi_endproc
.LFE1:
.size main, .-main
.ident "GCC: (Ubuntu 11.3.0-1ubuntu1~22.04) 11.3.0"
.section .note.GNU-stack,"",@progbits
.section .note.gnu.property,"a"
.align 8
.long 1f - 0f
.long 4f - 1f
.long 5
0:
.string "GNU"
1:
.align 8
.long 0xc0000002
.long 3f - 2f
2:
.long 0x3
3:
.align 8
4:
Lets look, if a simple loop is faster than a function pointer delegate call:
/* program looptest.c */
include <stdio.h>
const int b = 23;
// main
int main(int argc, char **argv)
{
int i = 0;
int a = 23;
/*
if (a < b)
printf("Value of a (%d) is lesser then value of b (%d)\n", a, b);
else if (a == b)
printf("Value of a (%d) is equal value of b (%d)\n", a, b);
else if (a > b)
printf("Value of a (%d) is greater than value of b (%d)\n", a, b);
*/
// iterate through for loop
for (i = 1; i < 4194304; i+=11) {
a = i;
if (a < b)
printf("Value of a (%d) is lesser then value of b (%d)\n", a, b);
else if (a == b)
printf("Value of a (%d) is equal value of b (%d)\n", a, b);
else if (a > b)
printf("Value of a (%d) is greater than value of b (%d)\n", a, b);
}
return 0;
}
/* program funcptrtest.c */
include <stdio.h>
const int b = 23;
// A normal function with an int parameter and void return type
void fun(int a)
{
if (a < b)
printf("Value of a (%d) is lesser then value of b (%d)\n", a, b);
else if (a == b)
printf("Value of a (%d) is equal value of b (%d)\n", a, b);
else if (a > b)
printf("Value of a (%d) is greater than value of b (%d)\n", a, b);
}
// main
int main(int argc, char **argv)
{
int i = 0;
/* fun_ptr is a pointer to function fun()
void (*fun_ptr)(int) = &fun;
is equivalent of following two
void (*fun_ptr)(int);
fun_ptr = &fun;
*/
void (*fun_ptr)(int) = &fun;
// call once with static int
// (*fun_ptr)(b);
// iterate through for loop
for (i = 1; i < 4194304; i+=11) {
// Invoking fun() using fun_ptr
(*fun_ptr)(i);
}
return 0;
}
Well, that's not so deterministic, of course our simple looptest.asm has a shorter assembler.
But execution time is not so huge difference, we have to simulate, that in many scenarios.
[To be continued ...]
2022-10-15
About identity & privacy
Most complete Identity of a person is defined / determined by different public, restricted or private accessible spheres.
2022-10-11
It's about creating distributed service oriented communications
Attention:
This article isn't about daily standard electronic communications via network protocols (e.g. email services or shared network folders), neither about user authentication / authorization nor groupware.
It's about:
Implementing or consuming customizable reliable distributed services;
by choosing & implementing a programmable extensible scalable, easily portable, standardized inter-compatible fail-safe resilient communication middleware, that's financially essential for most critical business processes.
For what kind of companies is that useful, important or relevant?
It's relevant for all companies, that consume many crtical data from external partners / service providers;
then process received & own data inside different departments (maybe in different locations) with different areas of responsibility (e.g. fraud detection, critical real-time scaling of dynamic hardware (memory, harddisks and available CPUs, permanent risk adjustment and last but not least anonymized [General Data Protection Regulation] precise reporting for legal reasons);
finally and ultimately share processed data to maybe different external organisations with very deviating requirements, like government fraud reporting agency on one side and partners inside a foundation or joint umbrella organization however.
Overview most common distributed service oriented communication technologies in history
What technologies do you use in your company / organisation or as private person for distributed service oriented communication?
- antique: [ 1980s ]
- Sun RPC [ remote procedure call ]
- old: [ around the millennium ]
- DCOM [ Distributed Component Object Model ]
see also: ActiveX, DDE, .NET Remoting - Java Corba
- message oriented middleware [ mostly XML based ]
- SOAP / XML based Webservices [ SOAP message ]
- .NET Webservices + Web Services Enchancements (.asmx .ashx )
- Previous generation: [ since 2010 ]
- WCF [ Windows Communication Foundation ] by Microsoft .NET
- Swagger [ swagger.io swagger-api ]
- Rest API [ Representational State Transfer ]
- RestFul web api
- Apache CFX [ cxf.apache.org ]
- gRPC [ gRPC Remote Procedure Calls ]
gRPC [ grpc.io | github.com/grpc ] was initially created by Google
What local software suites / solutions / products and enterprise cloud services are included in your distributed service oriented communication(s workflows)?
- Microsoft BizTalk Server
- RabbitMQ [ github.com/rabbitmq ]
- Amazon Web Services [ aws ]
- Azure RestAPI Reference
[ to be continued ... ]
-

.png/1200px-Flag_map_of_Divided_Korea_(1945_-_1950).png)



_k%C3%B6zn%C3%A9l._Harck%C3%A9ptelenn%C3%A9_tett_ISU-152-es_szovjet_rohaml%C3%B6vegek%2C_a_h%C3%A1tt%C3%A9rben_egy_T-34-85_harckocsi._Fortepan_24854.jpg/330px-J%C3%B3zsef_k%C3%B6r%C3%BAt_a_Corvin_(Kisfaludy)_k%C3%B6zn%C3%A9l._Harck%C3%A9ptelenn%C3%A9_tett_ISU-152-es_szovjet_rohaml%C3%B6vegek%2C_a_h%C3%A1tt%C3%A9rben_egy_T-34-85_harckocsi._Fortepan_24854.jpg)