(Draft)
Monolopy (Conspiracy theory warning)
In mercantilism owning and potentially using a monopoly was considered as tactical advantage. Think about it, that China soonly has a monopoly on a lot of industrial products, but most of China's hardware exoported have an american, south korean or japanse label.
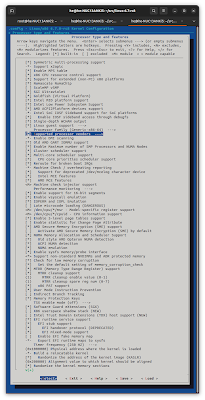
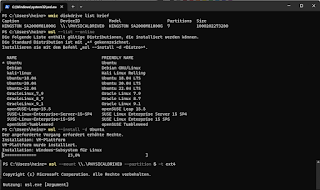
When there might be a common closed source smart phone. personal computer or smart phone with only one operating system with market dominance over 90%, then we might run into a trap.

If later then, disassembling, reversing engineering is punished with high penalties and international legal claims, then social credit program can be introduced step by step by backdoor.
If your social credit is negative, then you might not have all functions enabled (on your monopoly phone or monopoly personal computer) (THIS MIGHT BE VERY DANGEROUS)
Attention, Huawei, Chinas biggest smart-phone brand and ready to soonly be main player also in african markets, is still android and open based on open source linux and I don't claim, that China will use such practices. But there is no guarantee, that US or Chinese companies would develop or exrend their powers to collect more data or control more individuals in entire world by monitoring them permanently.
In open system, you can choose a other os to install on every hardware. I remember, that Sony Playstation implemented an other OS bootloader, where you could run linux on it. The community demanded it. Today no one tries to recommand LineageOS compatbility on Smart-Phone hardware.
Balances & checks for free democracies
Freedom of media index
Multiple independant print & internet media or different media blocks. +1
Fact-Checking in more serious media. +0,5
Double Fact checking, interviewing all stakeholders. +0,5
Different TV stations and radio stations in country.. +1
Access to satellite tv or streamed news in internet +1
Access to different ISPs. foreign western Proxy Services, entire Internet and Tor Onion Router +1
Possibility to blog, moderate in blogs and internet media and not permanently censhorship (censorship, when hawkishing a little bit to much for hours until 1 week is OK). +1
Possibility to report over public events in blogs, media, internet media like X or Facebook, you need special permission and agreement from company, private person and NGO, when reporting inside over companies, NGOs, military and private persons private sphere (concerning e.g. product placement, innovations, sexuality or belief). +1
Tolerate whistleblowing like in the US, when reporting over complicated human rights violences of foreign troops in war. +0,5
Storry telling, conspiracy theories and narratives are marked with a recognizable symbole, e.g. +0,5
Civil & business & companies rights
9 basic points
The word church in follwoing could also mean shrine, temple, stone circle, lgbt community or any religious monoment or place.
Freedom of assembly (if missing -4)
- Right for workers to join a labor union or representation of employees.
- Right for companies to join a free foundation or trade guild.
- Right to join a religious community or free church (no hierachically bottom up grassroot foundate non state church).
Freedom of speach, freedom of art and freedom of posts without state sanctions (exception national socialists content, radical djihadist content, stalinist content in some countries) (if missing -4)
Right to work self choosen and startup again after phase of unemployment. Right to work no matter what in company, NGO as free artist, freelancer, whatever ... (for some non free profession, like medical doctor or train man you need a special prooved certificate or degree) (if missing -4)
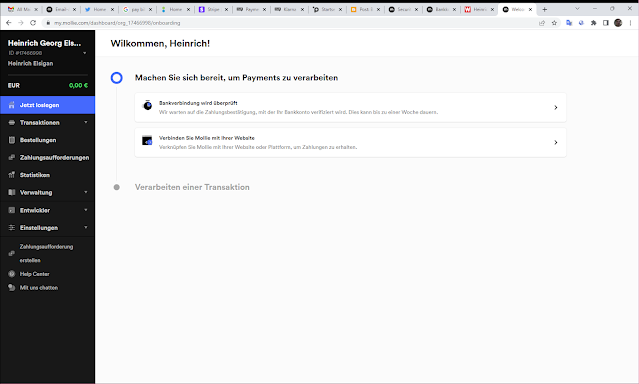
Right to found, own, buy (part of) a company or poperty, right to own stock market values, money, gold, derivates, freedom to choose bank and payment provider and freedom of trade (Excpet US patriot act or sanctions against countries as US ally) (if missing -5)
Right for worker to leave company (inside a certain time period, normally 0-3 months) when getting a better offer without extreme high penality for joining another company. Right for companies to hire & fire women & men inside a certain time period (normally 0-3 months). (if missing -4)
Right to vote, right to protest and right to access basic state services for every citizen. (if missing -4)
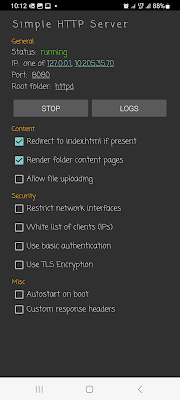
Freedom of operating system, freedom to choose between open & closed source and freedom to develop after a free choosen license, e.g. BSD, Apache, GNU, MIT, closed source). (if missing -4)
(Standardized licenses for paying and billing closed source, 3-10 categories would be nice, like renting software as a service like office 365, paying a cloud provider on network and CPU and storage using, installing a software and paying for year a guaranteed support, ...)
Right on abortion, if both mother & father agree to it, because otherwise they would be slaves, owned by a landlord in law. Free citizens should have that right. Don't bring slavery back to US. (if missing -5)
Right to have a own sexuality, freedom for adults to have sex if both agree (maybe after rules of their church), right to marriage (maybe after rules of a church or federal state). (if missing -3)
Right to adopt non adult childs, if parents or next familiars (if parents death) of children agree to it and have a permanently visiting right at least all 2 weeks. Maybe a free NGO check is needed, that this is good too. (if missing -3)
Non discrimination rights and possibility to protest against it or go to an independant court.
(In private companies I saw and experienced discrimination very rarley, but at civil services or police or public high schools, this is happening some times). (if missing -2)
Right of an independent and fair judgement (maybe right to have a second independant judge, if court is politically motivated). Right of comparison between companies or private persons (both agree that one pays the other a fee of 100US$ of causing pain per day) (if missing -3)
Right to wear waepons for veterans (who served at national army with locked and loaded waepons). (if missing -1)
Right for people over 16 to drive a car, ride a byke, bicycle (maybe a confirmed license is needed, horse, donkey, drink whiskey (of course not when riding or driving a vehicle) and smoking natural herbs, tobaco (but no opiods). (Maybe the right of your church doesn't allow some parts). (if missing -2)
Right to have a save and proper enviroment: State can ban bear, wolfes or elephant hunts or shutting birds or using animals for bio-nano technolgy experiments. (if missing -2)
Denied: Experiments with human beeings without their agreement (signed and 3rd party validated) (like milkram experiment) is forbidden. Long time studies of human beeings. (if missing -4)
Right to access independent technology to scan your genom and verify children and parents, if they agree. (if missing -2)
Social rights:
(For Europe, Great-Britain. Brazil and ???): Right of small social security (at least 1000US$ per month), if you get unemployed or need assistence. (if missing -3) (State money transfer over 150.000 US$ per year without doing anything is strictly forbidden. Excluded: Fees from private companies as a free services for long employment, excellent performance or great innovation or great ad value).
Right for every cirtizen to access as citizen public libraries with internet access with a legitimated identifying card.
Right to repair wikipedia, right of elected assembly to transfer special money to some urgently needed NGO task forces, like open source foundation, wikipedia, ...
Right for jobless people to getting courses to be ready for a new job, where they are only 40% - 80% qualified and not enough fit 4 work.
To be continued ...



![strace openssl s_client -starttls smtp strace openssl s_client -starttls smtp -connect [mailserver] [port]](https://blogger.googleusercontent.com/img/a/AVvXsEjTMio99QvTR7KVsaziVCR6fdBe7iA_7-NgdGxGkw0C7ikR8DqMUMx4eC0pCF-QHXUNQhkyjQhKK4yAWhRy9M1-698G8a1EmRDi5AdrUCfaekQyadu3GC71szP5YWQ35t7XDbKhEf9M0T6OcVneV8ml-rOi102n2ljk8kRNrhozOc5Mx5QyKA3t_2cGg3hU=w640-h336)